City officials in Atlanta are handling a cyber attack that uses ransomware to preserve internal laptop systems hostage.
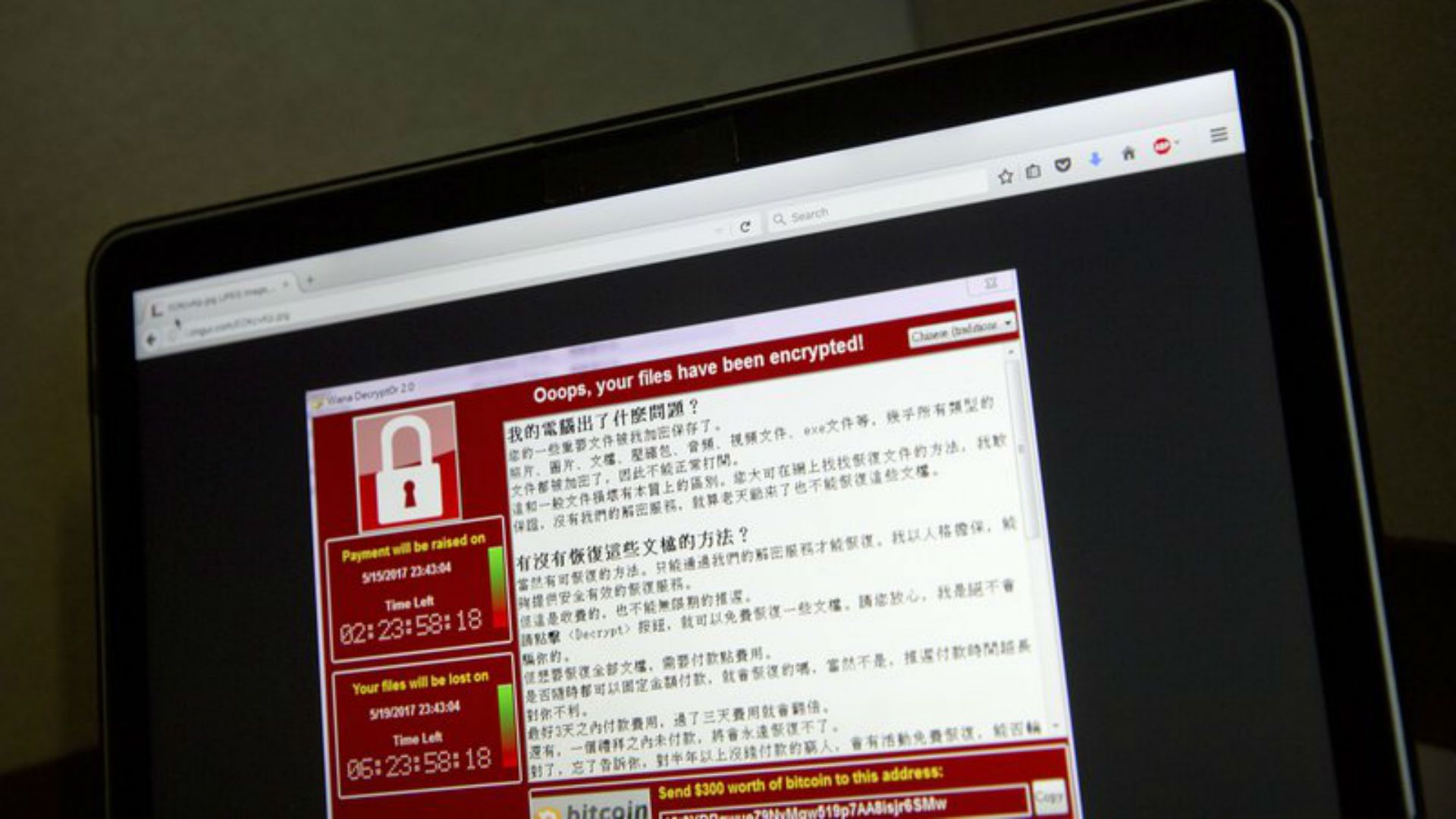
The assault brought on outages on numerous pc structures, along with online bill paying services and some regulation enforcement statistics, CBS affiliate WGCL-TV mentioned Thursday. A ransom observes determined Thursday morning stated that each one file on affected systems had been encrypted and demanded charge within the cryptocurrency bitcoin to decrypt them.how to decrypt ransomware files
Ransomware is malicious software that could lock up your documents till you ship hackers a ransom fee.
It featured in the WannaCry assaults in May and the NotPetya assaults in June, each of which swept via hospitals, banks, and governments in several nations. But after July, the fees of ransomware infections dropped sharply, in line with a record from Malwarebytes in January.
Atlanta Mayor Keisha Lance Bottoms told CBS News the town is receiving help from the FBI, Department of Homeland Security, Microsoft and Cisco Security.
It wasn’t at once clean if personal records were compromised, however authorities are encouraging town employees to be searching for signs that their statistics can also be stolen, like surprising credit score card prices.
The Benefits of Using Laptop Bags
Have you lately bought a laptop or pocketbook? Whether you load up your new PC or whether or not you snagged a mean one for an unbeatable fee, you’ve positioned your hard earned cash closer to something. Naturally, you want to guarantee the product’s safety, and as a computer through its nature is a portable entity, transporting it from vicinity to area must be achieved with relative ease and protection. Such capabilities are all advantages of the usage of computer baggage.
There are several key advantages of the use of a laptop bag. Many tours with their laptops and shop a number of crucial, paintings related facts on them. Transporting a pc without a few forms of the garage for it might now not be something any computer owner would appearance favorably upon. A bag to your pc allows to no longer only shield the device from the elements, but also provides a level of cushion. When journeying, your pc is certain to knock against something or be pressed in opposition to any other piece of bags, so having the essential padding round for safety is continually acceptable.
A computer normally requires several accessories to be carried in conjunction with it.
Another advantage of the usage of laptop bags is they usually offer sufficient room to shop any wires, portable mice, and many others. Additionally, there are lots of small garage spaces in which such things as portable flash drives, compact discs, and a collection of other media may be accommodated. Additionally, an adjustable strap makes it very handy to hold the bag at an individual’s personal comfort degree.
One of the blessings of using a laptop bag is regularly no longer taken into consideration, but it is one that could play to someone’s gain. Quite virtually, it is fashionable and is regularly seen as a hallmark of professionalism. Carrying a bag to your computer offers an individual a professional appearance, which will be beneficial in looking to set an effect of self-assurance and a commercial enterprise pushed attitude in environments which include process interviews and corporation conferences.
The decision of how a good deal to spend on a pc bag usually falls at the need
Frequency of use and what the user is searching out compartment clever. For the one’s computer proprietors who desire to have the maximum in all three regions cited above, the rate could be at the better cease. Those who want the computer bag sincerely for transporting the computer and do not bring the bag for lengthy periods of time, a less costly pc bag would be sufficient.
The Mountain and River Systems inside the Philippines

There are three large mountain levels in Luzon-the Caraballo del Sur, the Sierra Madre, and the Caraballo de Baler. The Caraballo del Sur extends from north to south and consists of the Central Cordillera and the Northern Cordillera. Its highest height is at the intersection of the boundaries of Abra, Ilocos Norte, and Cagayan.
The Sierra Madre also referred to as the Pacific Coast Range starts on the metropolis of Baler, and crosses the provinces of Cagayan, Isabela, Nueva Viscaya, and Quirino. The Sierra Madre is the longest non-stop mountain range in the Philippines.
The Caraballo de Baler extends from Baler, the capital of Aurora, and ends inside the San Bernardino Strait on the southeastern tip of Luzon. In this ranges are located Mayon Volcano in Albay and Bulusan Volcano in Sorsogon.
Also in Luzon are the smaller mountain levels of Zambales and Tagaytay. The Zambales Range begins at Cape Bolinao in Pangasinan, extends south alongside the coast of the China Sea, and ends within the Bataan provinces of Cavite and Batangas. Mount Makiling, in Laguna, and Taal Volcano in Batangas, are inside the Tagaytay Range.
In the Visayan region, Panay Island has a range stretching from north to south and separating the province of Antique from Aklan, Iloilo, and Capiz provinces.
The Principal Mountain Ranges in Mindanao
• Diwata Mountains – run alongside the Japanese coast of the island.
• Central Range – extends through the length of Mindanao following the western boundary of the Agusan and the Davos.
• The mountain ranges which form the spine of the Zamboanga peninsula and Misamis Occidental.
The maximum top in the Philippines is Mount Apo, in Davao del Sur, 2,954 meters above the ocean level. The second maximum is Mount Pulog inside the Bicol Peninsula, approximately 2,585 meters above the ocean degree. Other superb Philippine mountain peaks are Makiling, Banahaw, and San Cristobal-all in Laguna-Arayat in Pampanga, Mayon in Albay, Baco in Mindoro Occidental, Matalingajan in Palawan, and Makaturing in Lanao del Sur.
What Is Ransomware?

For several years now, ransomware attacks were progressively increasing. Back in 2013, CryptoLocker hit the headlines as one of the first ransomware applications to be released. Until 2014, when its distribution networks had been taken down, CryptoLocker wreaked havoc infecting infinite personal and enterprise computer systems. Since then, there were many new ransomware infections, a number of which use the CryptoLocker call but are in truth one-of-a-kind programs. In this post, we give an explanation for what ransomware is, the effect that it can have on your enterprise and what you could do to guard yourself towards the chance.
Ransomware is a shape of malware.
Malware is a general time period for malicious software programs, commonly known as viruses, that are designed to enter our computers and different gadgets without our expertise or permission, and with the aim of causing harm to our devices and the information that lives on them. There are many exclusive varieties of malware and each has an exceptional impact. Some, for example, may also be designed so as to compromise our statistics, even as others will clearly cause damage to our devices.
Ransomware is a form of malware that has the potential to encrypt your documents, without your understanding, before disturbing charge for their return. Very often, there is additionally a time restriction imposed on the price. It’s vital to be aware that there’s no assurance that your documents may be decrypted as soon as payment has been made.
As nicely as focused on files containing precious personal or business information including pictures, spreadsheets, and documents, ransomware packages can also have the ability to lock down system files as properly, that can render packages, net browsers and even whole operating structures unusable. Although the authentic CryptoLocker infection centered Windows, the modern threat is not constrained to PCs. Macs and mobile devices with the Android operating device installed are also prone to ransomware infections.
The maximum common manner that ransomware is unfolded is through infected
Email attachments and links contained in Emails. Once an infected file has been opened, it is able to infect your device. It can be tough to detect files which might be infected because the malware is often hiding. The document extension may be changed and the malicious code is compressed into a zip file. Infection can also occur although installation of packages from untrusted or unknown publishers, as those may also incorporate ransomware. Once it has inflamed your gadget, ransomware works quietly within the historical past and connects to a faraway server to encrypt documents.
Once the ransomware has encrypted your documents, you’ll acquire a pop-up message annoying price. The amount of money that is demanded using ransomware packages varies drastically, ranging from a few hundred to several hundreds of kilos. It is not unusual for the price to have to be made in an nameless forex, together with Bitcoin. As previously stated, there’s no guarantee that your documents could be decrypted if you pay the ransom.
As you can in all likelihood consider, ransomware will have very serious effects for groups.
If you preserve sensitive inner and client facts to your systems, and it isn’t securely backed up, you’ll be at risk of losing it if your systems are inflamed with ransomware. If your records are backed up, you may be able to recover your crucial documents, however, this is going some distance from solving the trouble. You will still have experienced a probably very serious records breach, that can have some of the devastating outcomes of its personnel. It can price groups a sizable sum of money to cope with an information breach, which can also damage your reputation and lead to loss of business and doubtlessly even prison instances being brought against your organization.
